Changelog: How secure is America’s critical infrastructure?
Thomas Kelley / Unsplash
Welcome to Changelog for 11/16/2023, published by Synack! README senior editor Nathaniel Mott here with a quick programming note: I’m off next week to celebrate Thanksgiving, so there will be no Commit or Changelog, but we’ll return to our regular schedule on Monday, Nov. 27.
The payload
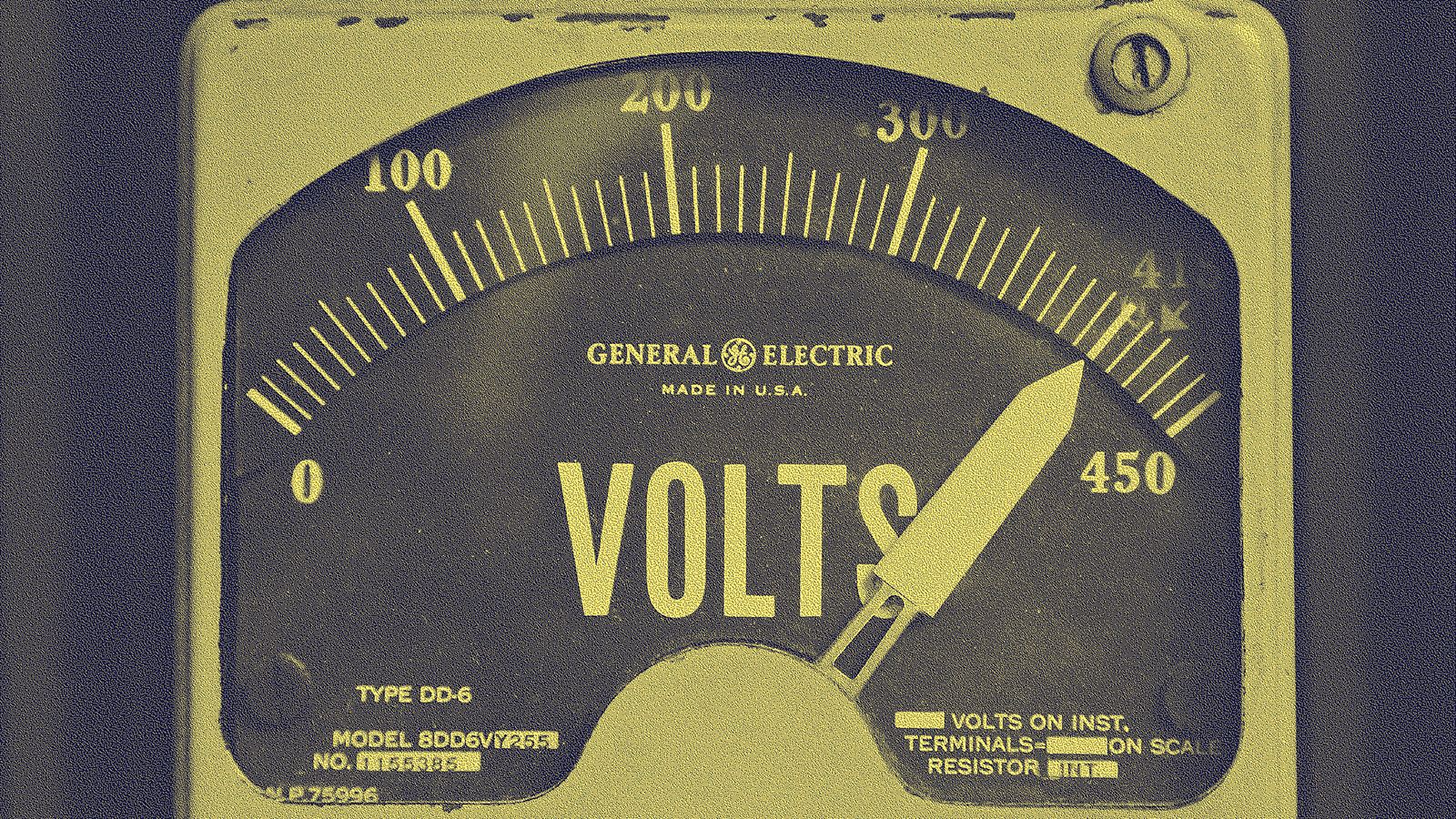
It’s that time of year—and I’m not talking about Thanksgiving feasts, snowball fights and holiday shopping. The North American Electric Reliability Corporation’s (NERC) Electricity Information Sharing and Analysis Center (E-ISAC) today discussed its latest grid security and resilience exercise, GridEx VII, which counted 250 organizations from the U.S. and Canada among its participants over the last two days. The biennial event typically throws the kitchen sink of simulated cyber and physical threats at its power grid participants to test their readiness for a real attack.
“While we're not aware of a specific credible threat that could potentially impact the power system, nonetheless, I'm sure you'll agree that the threat landscape is dynamic and continues to present challenges that are increasingly difficult to detect and defend against,” NERC senior vice president and E-ISAC chief executive Manny Cancel said today during a webinar devoted to discussing GridEx VII. “The electricity sector is under constant attack from nation-states and organized criminals.”
We’ve received two stark reminders of the threats the sector faces in the last week. The first, which I covered in last week’s newsletter, was Mandiant’s revelation that Sandworm hackers caused another power outage in Ukraine in October 2022. The second arrived this week when SektorCERT revealed that “Danish critical infrastructure was exposed to the most extensive cyber-related attack we have experienced in Denmark to date” after 22 companies were compromised in May.
Those incidents—along with the discovery of Industroyer2 and Pipedream control system-focused cyberthreats in 2022—make it clear that the electric grid remains a prime target for nation-state hackers. Global conflicts, including Russia’s invasion of Ukraine, have also exacerbated concerns about attacks on the grid. “Geopolitical turmoil has contributed to a dramatic uptick in malicious cyber activity,” Cancel said, “including new iterations of the malware and ransomware that constantly pressure information technology and operational technology platforms."
Cancel added that "we've also seen a marked increase in serious security incidents at electric utilities throughout the United States,” and although “most of these incidents do not result in great impact,” he said that E-ISAC and its partners “expect this trend to continue as we go forward.” The electricity sector will have to continue to collaborate with its government partners, Cancel said, to meet those challenges.
E-ISAC will share more information about GridEx VII’s findings in a March 2024 report.
The week, compiled
This section was originally going to be about Reptar, a vulnerability in recent Intel processors that was disclosed by Google earlier this week. (Here’s a link that goes into more detail on the nature of the vuln.) It’s an interesting security flaw that many organizations have to worry about; you should read more on it.
So why the shift? It’s because DataBreaches reported that AlphV claimed to have filed a complaint with the Securities and Exchange Commission after one of its victims, MeridianLink, failed to disclose that it had been breached by the ransomware gang also known as BlackCat.
A bit of background: The SEC announced in July that companies would have to disclose a breach approximately “four business days after a registrant determines that a cybersecurity incident is material.” That means affected organizations must be far more open about when their defenses have failed them.
Towfiqu barbhuiya / Unsplash
That’s interesting enough. (Especially for companies that prefer to keep incidents hush-hush.) But a ransomware gang filing a complaint with the SEC because one of its victims didn’t meet these requirements—even though my and DataBreaches’ understanding is that they aren’t expected to go into effect on Dec. 15—means that public companies have yet another thing to worry about after a hack. It’s like a burglar calling your insurance company after robbing your home to let them know you left your windows unlocked and your security system down.
Here’s the week in README:
README: Why look for vulnerabilities in finished software when you can try to compromise the developers creating it in the first place? Threat actors seem to be asking themselves that question more often lately, and they’re using a mix of dead-simple and surprisingly sophisticated methods to do so, regular contributor Robert Lemos reported in his most recent piece.
Commit 11_13_2023: A “nationally significant cyber incident” caused the closure of four Australian ports, initial fallout from LockBit’s hack of the Industrial and Commercial Bank of China, Boeing data was leaked, Malaysia disrupted a phishing-as-a-service platform and Google filed suit over ads used to serve malware.
Commit 11_14_2023: The FBI has identified (but not arrested) several members of the hacking group that popped MGM Resorts, the Royal ransomware gang is widely believed to have rebranded as BlackSuit, TA402’s exploit chains get increasingly complex and New York wants hospitals to beef up their security.
And some other stories worth checking out:
Wired: Ever wanted to learn more about how the Mirai botnet practically broke the internet? Wired’s Andy Greenberg has you covered with a new feature that delves into the lives of the three young hackers responsible for developing a botnet capable of knocking the world’s leading websites offline—and what happened next. It’s a gripping read that Wired temporarily made freely available to everyone.
BleepingComputer: IPStorm, which BleepingComputer described as “a proxy botnet enabling cybercriminals, scammers, and others, to evade blocks and remain anonymous by channeling their traffic through thousands of compromised devices in people’s homes, or offices,” lost its thunder. The Justice Department announced this week that the service was disrupted alongside the arrest of its creator.
404 Media: What do hackers do with the cryptocurrency they receive—either by stealing it directly or receiving it as a ransom—from their victims? 404 Media today reported that at least some of them use online casinos “to multiply and attempt to launder their ill-gotten gains.”
A message from Synack
How companies approach security testing is in need of a makeover. Traditional pentesting satisfied compliance requirements, but that doesn’t stop critical vulnerabilities from affecting the business. With a strategic testing approach, companies can discover the vulnerabilities that matter most, manage remediation more quickly and see security posture improvement in real time with essential analytics. Learn how to start your journey to strategic testing.
Flash memory
It seems like hackers used to have more fun. These days many of them have busied themselves writing ransomware, infostealers and wiper malware intended to be used in targeted attacks. Panda Burning Incense—a virus that spread throughout China in October and November 2006—was the opposite.
CSO reported in 2007 that Panda Burning Incense was so named because it targeted executable files and changed their associated icons “to an image of a panda holding three sticks of incense—a traditional way of praying in China”—in addition to working around “some security processes” and spreading “by attacking shared network resources.” It was malware, sure, but it also boasted a certain level of playfulness.
Not that its creators had much fun. The Register reported in 2007 that “police in central China's Hubei Province have detained eight men in their 20s alleged to have participated in the spreading” of the virus, which marked “the first time Chinese authorities have made arrests relating to a major virus attack originating from that country.” Maybe their lack of seriousness proved to be a problem after all.
But their arrest wasn’t the end of Panda Burning Incense. Reuters reported in 2009 that a variant of the malware that featured “a malicious component meant to make infection harder to detect,” which turned out to be a rootkit, was spreading throughout China. No more nonsense (or incense) allowed.
Local files
The Record: A bit of good news: The Record reported on Nov. 15 that “less than two months after a ransomware attack impacted St Helens Borough Council in northwest England, most services at the council are running again,” and the council said “further cyber hardening controls have been implemented and continue to be enhanced in coordination with the council's cyber security service provider.”
MPR: Schools in Minnesota “are turning to local taxpayers and state officials for help in building up their defenses” as they continue to be targeted by ransomware gangs and other cybercriminals, MPR News reported on Nov. 14, with the hope of receiving the additional funding required to improve their defenses.
Off-script
So it turns out the Premier League was a gateway drug. It’s no longer enough for me to watch England’s best teams compete every weekend—now I’m keen to watch matches from the Europe-wide Champions League as well as the Premier League analogues Bundesliga (Germany) and La Liga (Spain).

Tech Daily / Unsplash
It’s surprisingly hard to watch all this: Each league has sold its U.S. streaming rights to a specific platform. Peacock is the only way to catch Premier League matches, Paramount+ is the sole source for Champions League games and ESPN+ has called dibs on both the Bundesliga and La Liga. That means I need to pay for three services to catch all of these matches, and even though I’m mostly within Apple’s ecosystem, they all require dedicated accounts (and can carry password manager headaches). Oh, the trouble I’ll go through to catch the Beautiful Game!







