Changelog: U.S. cyber leaders warn of China threat

Emmanuel Appiah / Unsplash
Welcome to Changelog for 2/1/2024, published by Synack! README senior editor Nathaniel Mott here with yet another cold… and, of course, the hottest cybersecurity news of the week.
The payload
The heads of the NSA, FBI, Office of the National Cyber Director and Cybersecurity and Infrastructure Security Agency (CISA) told the Select Committee on the Chinese Communist Party (CCP) on Jan. 31 that China represents an ongoing threat to U.S. critical infrastructure and economic development.
The infamous Office and Personnel Management hack of 2015 was brought up almost immediately; so were reports that China-linked threat actors have been making their way into the networks of energy providers, water management facilities and other critical infrastructure. Concerns about the privacy risks posed by TikTok were also discussed, which makes sense, given that the Chinese-owned platform has been banned from all U.S. government-issued devices.
FBI director Christopher Wray’s testimony seems to have made the most waves. Shortly after describing a successful effort to remove the “Volt Typhoon” threat actor from infected routers throughout the U.S.—more on that later—Wray said that “there’s a whole lot more to do” and that the FBI needs Congressional help to do it.
“To quantify what we’re up against, the [People’s Republic of China] has a bigger hacking program than that of every major nation combined,” Wray said. “In fact, if you took every single one of the FBI’s cyber agents and intelligence analysts and focused them exclusively on the China threat, China’s hackers would still outnumber FBI cyber personnel by at least fifty to one.” (And then, as expected, he used that threat to argue that Congress should continue to invest more in the FBI’s cyber capabilities.)
Wray’s sentiment was echoed by outgoing NSA and CYBERCOM director Gen. Paul Nakasone, CISA director Jen Easterly and National Cyber Director Harry Coker, Jr., all of whom said that the Chinese government represents a serious and ongoing threat to U.S. interests.
Easterly referenced the Colonial Pipeline attack of May 2021. “Americans couldn’t get to work, they couldn’t take their kids to school, get folks to the hospital. It caused a bit of panic,” she said. “Now imagine that on a massive scale. Imagine not one pipeline but many pipelines disrupted, telecommunications going down so people can’t use their cellphone, people start getting sick from polluted water, trains get derailed, air traffic control systems, port control systems are malfunctioning. This is truly an ‘everything, everywhere, all at once’ scenario, and it’s one where the Chinese government believes it will likely crush American will for the U.S. to defend Taiwan in the event of a major conflict there.”
The full hearing is available on YouTube. These don’t often make for particularly interesting viewing—especially when the bureaucracy and tribalism of U.S. politics collides with these directors’ efforts to just do their jobs—but this one was an exception despite mostly reiterating known talking points.
The week, compiled
Let’s talk about Volt Typhoon. Reuters reported on Jan. 29 that the “U.S. government in recent months launched an operation to fight a pervasive Chinese hacking operation that compromised thousands of internet-connected devices,” with the FBI and Department of Justice recently seeking and receiving “legal authorization to remotely disable aspects of the Chinese hacking campaign.”
Those efforts were officially recognized on Jan. 31. The Wall Street Journal reported that U.S. officials said Volt Typhoon’s efforts were “part of an evolving and increasingly worrisome campaign by Beijing to get a foothold in U.S. computer networks responsible for everything from safe drinking water to aviation traffic so it could detonate, at a moment’s notice, damaging cyberattacks during a future conflict.”
The acknowledgement of those efforts was accompanied by a new Secure by Design alert from CISA and the FBI that asked manufacturers of routers designed for small offices or home offices (SOHO) to finally take the security of their products more seriously. (I’d love to hear these companies’ arguments for why that isn’t feasible when their products are reportedly being used to stage potentially devastating attacks.)

Paul Hanaoka / Unsplash
Until those manufacturers heed these agencies’ warnings, however, the FBI and its partners will probably have to continue to surreptitiously remove malware from consumer devices. That doesn’t seem like a sustainable approach to securing U.S. critical infrastructure—to say nothing of the many individuals whose networks are being compromised in the process—even before you consider the broader implications of the FBI’s ability to remotely access the systems Americans use to go online.
And now for some of the other biggest stories of the week:
Ars Technica: Scammers are bridging the gap between cyberspace and meatspace. The FBI said this week that cybercriminals have been augmenting their existing schemes—which often sees them convince their victims they’ve been hacked and their financial assets are in danger—with instructions to take out cash so it can be picked up by a courier who lends a facade of legitimacy to the incident.
Mandiant: Speaking of Ars Technica, Mandiant said this week that the site’s forums were used by a group it tracks as UNC4990 to distribute additional payloads to systems that have already been compromised, typically via an infected USB device. Ars wasn’t alone in unwittingly hosting those secondary payloads, however; UNC4990 also hid its malicious code in files hosted by GitHub, GitLab and Vimeo.
BleepingComputer: Some 45,000 servers running the Jenkins continuous integration / continuous deployment software were susceptible to a vulnerability that could be exploited to achieve remote code execution, BleepingComputer reported on Jan. 29, despite warnings of publicly available exploits arriving last week. Here’s to hoping those admins patch against these vulns sooner rather than later.
A message from Synack
Pentesting on a FedRAMP Moderate Authorized Platform. Synack has achieved the Moderate "Authorized" designation from the U.S. Federal Risk and Authorization Management Program (FedRAMP), demonstrating that Synack's premier security testing platform meets the cloud compliance framework's rigorous requirements at the Moderate level. The milestone approval means government agencies can deploy Synack's best-in-class penetration testing and vulnerability management solutions – even for internal data, and in systems that process Controlled Unclassified Information. To learn more about the news and your security testing options, head over to https://hubs.ly/Q02jpBQ30.
Flash memory
Rather than looking back a few decades, for this week’s installment of Flash memory I decided to look at the biggest infosec stories from this time last year. My first Changelog for February 2023 was headlined “Passing the buck in cybersecurity, unleashing managed Chromebooks and ransomware attacks on schools” and focused on CISA director Jen Easterly and executive assistant director for cybersecurity Eric Goldstein arguing in Foreign Affairs that it was time for companies to finally take cybersecurity seriously.
I said the crux of their argument was that “Americans have not only ‘unwittingly come to accept that it is normal for new software and devices to be indefensible by design’ but also watched as ‘many organizations and companies [relegate] cybersecurity to the ‘IT people’ or to a chief information security officer’ who ‘are given this responsibility, but not the resources, influence or accountability to ensure that security is appropriately prioritized against cost, performance, speed to market and new features.’”
At this point I should acknowledge that everything is still terrible—as evidenced by the continued publication of this newsletter, which is predicated upon security being an ongoing concern, rather than a solved problem—a year later. And it’ll probably still be terrible a decade later. But I wish that organizations would take Easterly and Goldstein’s argument to heart. The world would be a better place (at least so far as security and, therefore, privacy are concerned) if they did. Let’s check back in next year.
Local files
The Register: SolarWinds thinks the Securities and Exchange Commission is being a bit of a bully. The Register reported on Jan. 29 that the company had “accused America's financial watchdog of seeking to
‘revictimise the victim’ after the agency sued it over the 2020 attack.” Its lawyers also said the SEC’s case against SolarWinds CISO Tim Brown is “not only unwarranted but inexplicable.”
KrebsOnSecurity: Brian Krebs reported on Jan. 30 that a recently arrested Florida man is believed to be “a key member of a criminal hacking group blamed for a string of cyber intrusions at major U.S. technology companies during the summer of 2022.” (Two groups, actually, both Scattered Spider and 0ktapus.) Krebs, as usual, has a full report on the accused’s online personas and suspected activity.
Access Now: Access Now, Citizen Lab and their partners today published an investigation that “reveals staggeringly widespread use of Pegasus to hack and spy on [Jordan]’s journalists, political activists, civil society actors, and human rights lawyers” between 2019 and 2023 “amid escalating repression and a crackdown on civic space, press freedoms, and political participation” within the country.
Off-script
I’ve been using NixOS, a Linux distribution built around the Nix package manager, for about a week now. There’s a lot to like about the distro: being able to declare pretty much every aspect of the system in a single “configuration.nix” file is lovely, the ability to easily boot into previous builds of the operating system has already proved useful and the package repository includes every piece of software I’ve wanted to use. It’s also much easier to see how my system is configured than it was with a distro like Arch or Fedora.
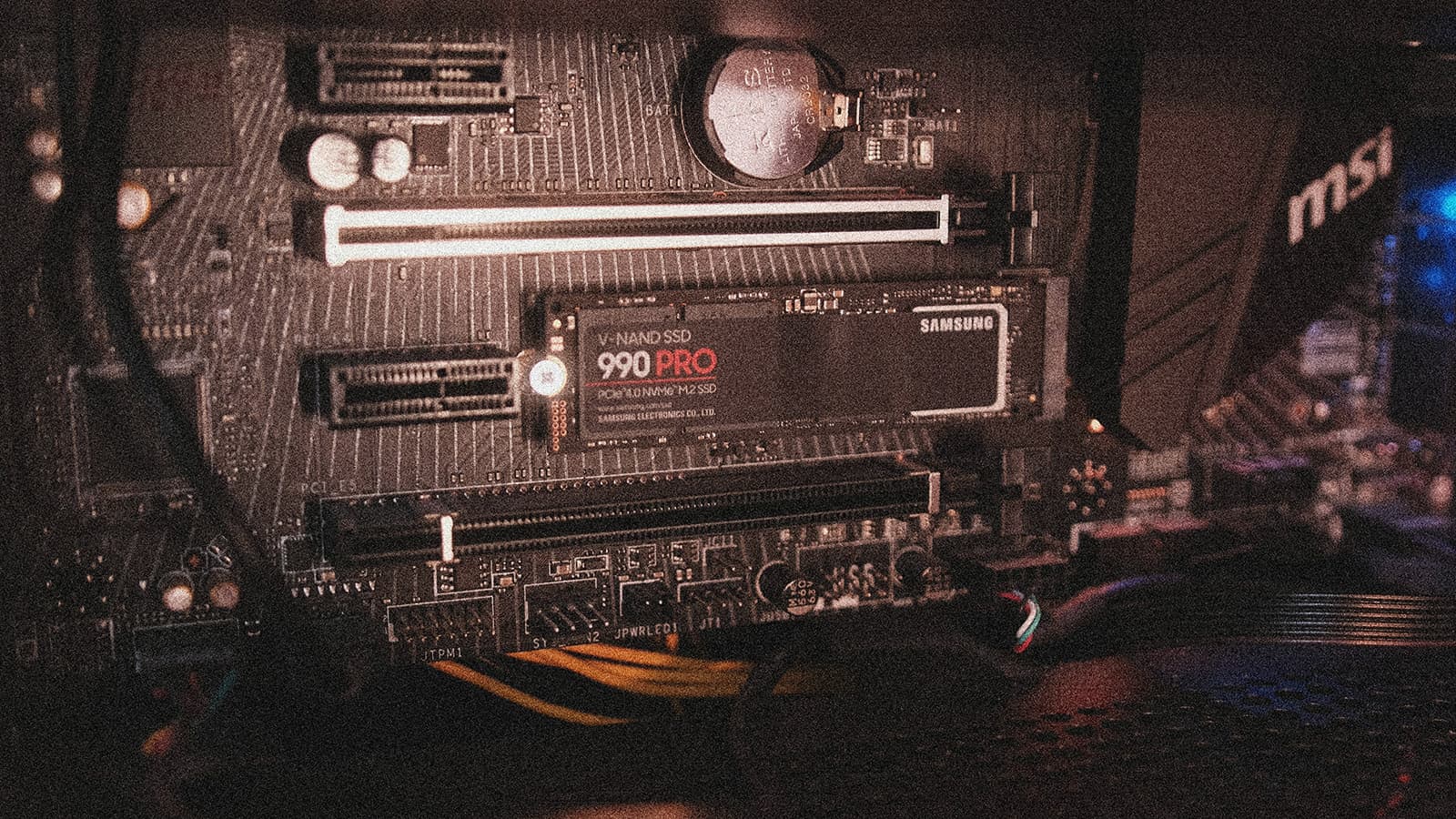
Samsung Memory / Unsplash
Yet for some reason I’ve been drawn to some other Unix-like operating systems—namely FreeBSD and OpenBSD—over the last few days. Maybe it’s because they’re complete operating systems rather than a combination of the Linux kernel, systemd, the Nix package manager and the GNU coreutils. Maybe it’s because of the BSDs’ cute mascots. (Provided you consider a pufferfish “cute.”) Or maybe it’s the extensive documentation maintained by both of the BSDs, which is currently lacking for NixOS.
No matter the reason, for now I am simply repeating the mantra “I must not wipe my SSD every time I feel like experimenting with a new operating system”... followed by “I must not buy another SSD just so I can experiment with a new operating system.” I guess it’s just mantras the whole way down.







