Web3's security dilemma, AcidRain malware and a cyber defamation case

ETH/Public Domain
Welcome to Changelog for 4/3/22, published by Synack! I’m your host, Blake, and I can’t believe this is already edition №10. If you enjoy this newsletter, I hope you’ll share it with friends and colleagues. Last week brought another massive crypto heist, revelations about wiper malware in the Ukraine conflict, and insights from the researcher behind the Conti leaks. Here’s the latest:
The payload
Hackers have siphoned off a staggering $625 million from the Ronin network in the latest breach to rock the cryptocurrency community.
The Ronin network supports a “sidechain” to enable Sky Mavis’s blockchain-based video game Axie Infinity, a popular Pokémon-like pet and trading adventure that incorporates nonfungible tokens while aiming to curb some of the environmental impacts of relying on transactions within the confines of the Ethereum network.
I’d flunk a pop quiz based on the previous sentence. When infosec pro Jackie Singh wrote about Web3 Luddites in a two-part series for README, she may well have been describing me.
Singh’s calls for infosec practitioners to learn the ins and outs of Web3 to head off more cryptocurrency heists and other threats are rooted in something of a cyber Hippocratic Oath: the infosec community should curb cybersecurity risks wherever they appear. Yes, even for the networks underpinning a game like this:

Blockchain technology can offer some structural security advantages, but you wouldn’t know it from reading about breach after breach at DAOs, cryptocurrency exchanges, and bridges.
I don’t need to have any interest in Ethereum, USDC or NFT video games to recognize that $625 million is a ton of money, and stealing it is not OK. So I’d like for security pros to heed Singh’s calls to help protect Web3’s growing user base, even if they don’t trade any “Axies.”
The week, compiled
And then there were seven: A disruptive hack of European satellite connections in late February was the work of yet another “wiper” malware deployed in connection with the Ukraine conflict, cybersecurity researchers said last week.
The “AcidRain” malware marks the seventh such destructive malware sample, analysts at SentinelOne noted in a report Thursday. The attack tool wiped out thousands of Viasat KA-SAT modems and routers, leaving many Ukrainians without internet service and mucking up communications for more than 5,000 wind turbines in Germany.
SentinelOne principal threat researcher Juan Andres Guerrero-Saade called the malware “the biggest elephant in the room” relative to the six other wipers, which have caused far less damage so far.
I’m sure AcidRain won’t be the last malicious tool to emanate from Russia’s ongoing invasion of Ukraine. I can only hope the next wiper malware won’t be any worse.
Here’s what played out last week:
CNN: The Ukrainian architect of a massive leak of data from the Conti ransomware gang spoke out about why he did it: Vengeance against Russia. “It’s my country,” the unnamed researcher told CNN’s Sean Lyngaas in a phone interview. “If they [the Ukrainian government] provide me weapons, OK, I’ll go fight. But I’m better at typing.”
Dark Reading: A nasty zero-day vulnerability (Spring4Shell) in the Spring Cloud web application framework rekindled fears about relying on open-source Java tools months after the bombshell Log4Shell vuln dropped.
Zero Day: Cybersecurity journalist Kim Zetter shined a spotlight on the Intrusion Truth team, whose aim is to expose Chinese state-sponsored hacking groups. “Intrusion Truth will not give up until China stops its large-scale and reckless cyber hacking,” a leader told Zetter.
Bloomberg: Hackers pretending to be law enforcement officials duped tech giants Apple and Meta into providing personal data from some customers, underscoring cyber risks posed by forged legal requests.
A message from Synack
Does your penetration testing meet compliance requirements? Synack recently announced it received Moderate “In Process” status from FedRAMP, meaning even more US departments, agencies and contractors can utilize its global network of elite ethical hackers for on-demand, around-the-clock pentesting. Find out more here.
Flash memory
One year ago, cybersecurity journalist Brian Krebs broke news of a “catastrophic” data breach and coverup at Ubiquiti, citing a “whistleblower” source who claimed hackers had stolen reams of sensitive data from Amazon Web Services databases housing source code and customer information from the router manufacturer.
But then evidence emerged that the supposed whistleblower may have actually caused the breach while attempting to extort his former employer. The Justice Department unveiled charges against onetime Ubiquiti senior developer Nickolas Sharp, claiming he leveraged his insider access to steal Ubiquiti data repositories and demand nearly $2 million in payment.
Sharp isn’t confirmed to have been Krebs’ original source for the March 2021 story. But Ubiquiti last week filed a defamation lawsuit against Krebs, claiming that the journalist doubled down on making “false accusations” against the technology company.
The case brought in Virginia will be one to watch for anyone who cares about the intersection of cybersecurity coverage and First Amendment rights.
Local files
StateScoop: A coalition of city-level chief information security officers is accelerating efforts to get cybersecurity resources from the federal government. “We are seeing the threat of international conflicts spill over into local governments who we are being told are the best targets,” San Francisco CISO Michael Makstman said.
FBI: In back-to-back private industry notifications last Tuesday and Wednesday, FBI authorities warned of threat actors targeting election officials, critical utilities and local government services with phishing campaigns and ransomware attacks.
The Dallas Morning News: Texas energy facilities are on high alert amid a series of U.S. government warnings about malicious cyber activity tied to the war in Ukraine. The grid there is “a rickety ship,” as one cybersecurity expert put it, and could be vulnerable to hackers.
Off-script
The U.S. Census released a trove of individual data from the 1950 census after a legally mandated 72-year wait.
I had luck using the free online search tool to find some of my old family members, including my grandma and grandpa, aunt and uncle on my dad’s side (he hadn’t quite been born yet):
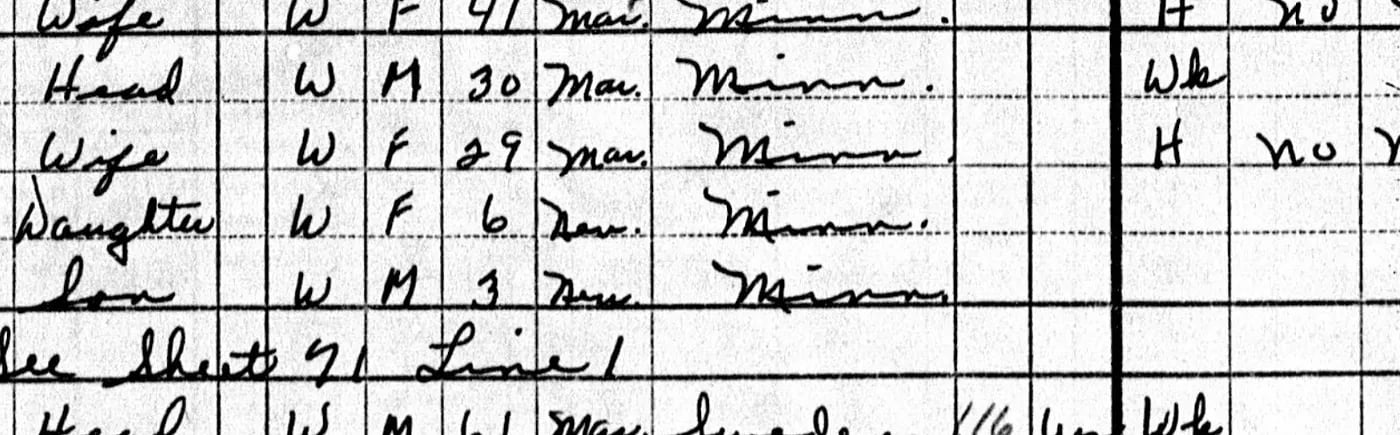
The handwritten documents offer a fascinating window on the past and are worth exploring.
That’s all for this edition— please send any tips, feedback and Web3 rants to bsobczak@synack.com. See you again next week!







