Changelog: Deja vu on the edge
Possessed Photography / Unsplash
Welcome to Changelog for 9/28/23, published by Synack! README senior editor Nathaniel Mott here following the launch of Commit—more on that later—with the week’s top infosec news.
The payload
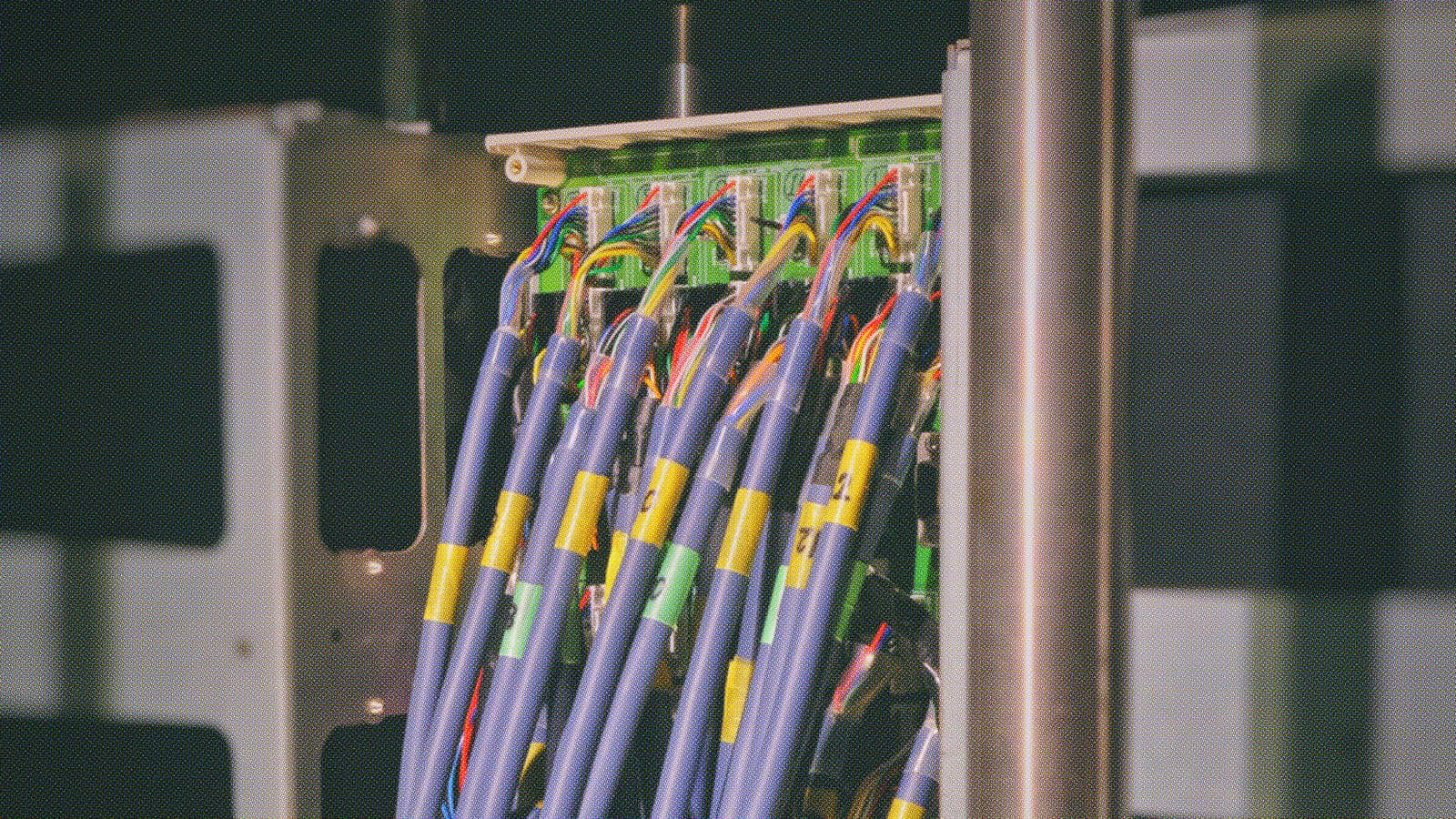
A coalition of U.S. and Japan’s cyber agencies said in a joint advisory published on Sept. 27 that a Chinese government hacking group, BlackTech, “has demonstrated capabilities in modifying router firmware without detection and exploiting routers’ domain-trust relationships for pivoting from international subsidiaries to headquarters in Japan and the U.S. — the primary targets.”
BlackTech has reportedly “targeted government, industrial, technology, media, electronics, and telecommunication sectors, including entities that support the militaries of the U.S. and Japan,” using “custom malware, dual-use tools, and living off the land tactics, such as disabling logging on routers, to conceal their operations.” (The report has a breakdown of the group’s tactics, techniques and procedures.)
Targeting routers is the latest example of adversaries going after so-called “edge devices” that sit on the periphery of a target organization’s network. As README reported before, threat actors often target these devices because they can provide a foothold onto target networks without attracting unwanted attention from defenders, many of whom lack visibility into what’s happening on these systems.
Will this advisory be enough for organizations to start taking the security of their edge devices more seriously? Probably not. But it’s yet another straw to add to the pile, and one of ‘em is bound to break the camel’s back.
The week, compiled
Reset the “number of Changelog installments that don’t mention the Storm-0558 hack” counter.
Reuters reported on Sept. 27 that, according to “a Senate staffer” who “attended a briefing by State Department IT officials,” the China-linked threat actors made off with tens of thousands of emails when they made their way into the Exchange accounts of various U.S. government agencies in May.
“The officials told lawmakers that 60,000 emails were stolen from 10 State Department accounts,” Reuters reported. “Nine of those victims were working on East Asia and the Pacific and one worked on Europe, according to the briefing details shared via email by the staffer, who declined to be named.”

Turag Photography / Unsplash
That’s just a fraction of the compromised emails. We learned in July that email accounts associated with the Commerce Department were also compromised by Storm-0558, and in August, Rep. Don Bacon (R-Neb.) said the FBI told him Chinese hackers had also gained access to his email.
I expect additional information about the hack’s extent to be revealed in the coming weeks and months. In the meantime, here’s what we’ve been up to at README this week:
README: The U.S. government is pleading with developers to dump memory-unsafe programming languages like C and C++ in favor of their memory-safe counterparts, Robert Lemos reported, in a bid to eliminate an entire class of vulnerabilities. But many of the most-exploited vulns aren’t memory safety flaws, and the hype around languages like Rust far outpaces their rate of adoption in professional settings.
Commit 09_25_2023: Monday kicked off with dueling reports about the group believed to be at least partly responsible for hacking MGM Resorts, Caesars Entertainment and other companies. Many have attributed the attacks to a group called Scattered Spider, but that might not tell the whole story. Also in this Commit: Predator spyware resurfaces, MOVEit Transfer victims come forward and a $200 million crypto heist.
Commit 09_26_2023: Tuesday brought us a pair of reports on how Immigration and Customs Enforcement and the Defense Counterintelligence and Security Agency rely on private companies for data used to surveil migrants or identify people who might target “America’s trusted workforce and trusted workspaces.” Also in this Commit: a max-severity vulnerability in libwebp, a ransomware-as-a-service affiliate and yet another reason to be wary of search results, especially when you’re looking for popular software.
And here are some of the other noteworthy stories of the week:
BleepingComputer: An extortion group known as RansomedVC told BleepingComputer that it “had breached Sony's networks and stolen 260 GB of data during the attack that they are attempting to sell for $2.5 million.” Another group called MajorNelson has also claimed responsibility for the attack, though,, and Sony would merely confirm that it’s “investigating the situation.”
Ars Technica: A proof-of-concept attack known as GPU.zip can be used by malicious websites to “read the usernames, passwords, and other sensitive visual data displayed by other websites” by exploiting flaws in the ways all major GPUs compress data to improve performance. Ars Technica’s report has more on why this is, how the flaw can be exploited and why this isn’t as big a threat as it seems at first glance.
A message from Synack
Dive deep into the top software flaws of 2022 in Synack’s inaugural State of Vulnerabilities report. Researchers on the elite Synack Red Team uncovered a record 14,800 exploitable vulnerabilities across Synack targets last year, ranging from authentication failures to SQL injections. The report shares insights into the root causes of these security gaps. Learn how Synack finds the vulnerabilities that matter and check out the full report here.
Flash memory
The GNU Project celebrated its 40th anniversary on Sept. 27.
Relatively few people are probably aware of GNU, and of those who are, it’s most likely because they encountered the GNU/Linux copypasta. But the project is no meme; it’s a core part of practically every computer on the planet. (Even if there are technically operating system distributions that are GNU-free.)
So what is the GNU Project? Simply put, it’s “a collection of many programs: applications, libraries, developer tools, even games,” that can be found in a variety of operating systems. Without GNU—or modern alternatives like musl and busybox—the Linux kernel would be unusable.
Much of the software people use also interacts with the GNU Project in some way. A lot of it was probably built using gcc, and even if it wasn’t, there’s a good chance it relies on glibc to interact with the host operating system. GNU’s not Unix, but it’s definitely ubiquit…ix.
Local storage
CyberScoop: Russian hackers may have shifted their focus a bit. CyberScoop reported that Russia has been focusing “on targeting Ukrainian law enforcement agencies to gather information about Ukrainian investigations into war crimes and counter-intelligence efforts against Russian spies and collaborators.”
The Record: Philippine Health Insurance Corporation said last week that it had discovered a cyber incident, and The Record reported that in the days since, it “has struggled to recover from a ransomware incident that forced it to take several websites and portals offline.”
Off-script
Counter-Strike 2 is out.
After a decade of Counter-Strike: Global Offensive, Valve has replaced its tactical shooter with a new title built on top of its Source 2 engine. The changes range from the cosmetic (everything looks like it’s been run through an Instagram filter) to meta-breaking (modifications to fundamental aspects of the game such as its tick rate, the way utility works, etc.) and it’s going to take the community a while to adapt to them.

ELLA DON / Unsplash
I’ve only played for a few hours—not this morning, of course, no—but so far I’m digging some of the changes. Mostly I’m just glad I can play Counter-Strike 2 on Linux. I used to play a lot of Valorant, but that game is only available on Windows, and its anti-cheat isn’t forgiving enough to allow me to play it in a virtual machine. So I’m excited to play Valve’s followup to one of the most storied games in esports history.







