Death by digital: attacks on healthcare put people at risk

Marcelo Leal / Unsplash
At least one person has died as what was arguably the direct result of a digital attack on a hospital, but cybercriminals seem unlikely to stop.
On Thursday, Aug. 3, an attack by a cybercriminal group against one healthcare organization led to widespread outages at hospitals and healthcare facilities in at least five states.
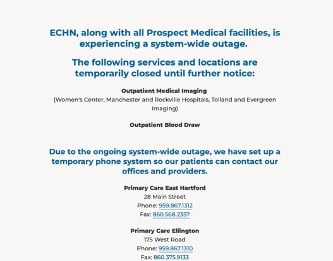
The attack on California-based healthcare conglomerate Prospect Medical Holdings resulted in the cancellation of scheduled procedures, disruptions to imaging and blood-draw services and a move back to paper records.
"Upon learning of [the breach], we took our systems offline to protect them and launched an investigation with the help of third-party cybersecurity specialists," the company said in a statement posted to a facility's website. "While our investigation continues, we are focused on addressing the pressing needs of our patients as we work diligently to return to normal operations as quickly as possible."
Three weeks later, many of the Prospect Medical facilities remain disrupted. Medical imaging at five Connecticut hospitals and outpatient facilities and outpatient blood draw services continued to be closed as of Aug. 22, and other medical facilities continued to use paper records, according to the Eastern Connecticut Health Network website. The FBI has opened an investigation into the attack.
So far, the outage has not directly led to a death. But there’s no guarantee that will continue to be the case—a cyberattack has, arguably, already led to at least one death.
In June 2019, a mother delivered a baby at Springhill Medical Center in Alabama, which had suffered outages of medical equipment due to a ransomware attack that disrupted operations for more than a week. The baby was born with the umbilical cord wrapped around its neck, which would normally have been detected by fetal heart monitors and led to a caesarean-section delivery. While the monitor in the room was operating, the fetal tracing information was not accessible at the nurse's station — a deficiency that would likely have led to the condition being caught, according to a lawsuit filed by the mother.
Ransomware and "excess deaths"
Ransomware works by stealing and encrypting data and then demanding payment based on the threat of the continued disruption of operations and the exposure of the organization to legal repercussions from data leakage. The massive NotPetya worm attacks showcased the potential impacts of ransomware outages: Drugmaker Merck suffered widespread outages leading to an estimated $1.4 billion in losses, while shipping firm Maersk had to shut down its own facilities leading to more than $300 million in losses, damaging 49,000 computers.
In a healthcare setting, ransomware also leads to a disruption of operations, but because of the critical nature of hospital works, disruption has the potential to lead to loss of life. At the very least, disruptions cause healthcare conditions within the healthcare system's region to worsen, Ty Greenhalgh, an industry principal in healthcare for device-security provider Claroty, told README.
"When a ransomware attack brings down systems at a hospital, it's a regional impact, not even just on that hospital where you're not able to deliver care, but it's regional, like a pebble in a pond," he said. "The consequences are spreading outward, because you've started diverting ambulances, ... patient waiting times go up, and people just leave. It's a quality-of-care issue ... and not just because people are necessarily dying."
That probably happened during the coronavirus pandemic, according to an analysis carried out by the US Cybersecurity and Infrastructure Security Agency (CISA). Disruptions caused by cyberattacks results in canceled and delayed surgeries, cancer treatments and diagnostic imaging. The ransomware attack on Prospect Medical Holdings showed that blood draws — a critical diagnostic tool — are not immune to the impact of cyber incidents, either.
CISA's analysis showed that multiple stressors impacted the healthcare system's ability to provide ideal care and likely lead to "excess deaths."
"Although there are no deaths directly attributed to hospital cyberattacks, statistical analysis of an affected hospital’s relative performance indicates reduced capacity and worsened health outcomes, which can be measured in the time of the COVID-19 pandemic in excess deaths," CISA stated in its report, Measuring the COVID-19 Pandemic’s Effect on the National Critical Function 'Provide Medical Care', adding that disruptions often lead hospitals to divert patients to more remote facilities, which also raises mortality. "In critical care, where minutes or hours can determine the survival rate of a patient — such as heart failure — diversions can drastically reduce survivability and recovery."
Cyberattackers see soft, willing targets in healthcare
During the coronavirus pandemic, several cybercriminal groups claimed that their "members" would not target healthcare organizations — apparently seeing the potential for causing deaths too unpalatable. However, even if that particular consortium abided by those limitations, most cybercriminals have no qualms. Healthcare is currently the No. 2 industry targeted by attackers measured in both attack attempts — finance is the most targeted by that measure — or by unique attacks, where government is most targeted, according to security firm Blackberry's 2023 Global Threat Intelligence Report.
Cyberattackers see healthcare institutions as soft targets and bet that the urgent need for hospitals to remain in operation will lead to quick payments following successful attacks, Dmitry Bestuzhev, senior director of BlackBerry’s cyber xthreat intelligence team, told README.
"Many hospitals and many health care providers, they run on a very opposite of old and outdated software," he said. "They're not like regular machines, where you can go and install Windows 11 and bring all the patches. Having like a huge network of such devices connected in a hospital, or any other place, it makes it really vulnerable to many attacks."
On average, approximately 60% of healthcare firms see at least one attack every year, and about three-quarters (73%) of those attacks result in data encryption, according to an annual survey of 3,000 companies — and nearly 250 healthcare organizations — funded by cybersecurity firm Sophos.
Exploits, Stolen Credentials, Phishing
The attacks also underscore the continued complexities in secure healthcare organizations. Unlike businesses, healthcare organizations cannot just put their consumers' data in a secure vault and restrict access. Doctors need access to patient records in a timely manner, and sometimes — such as in emergencies — they need access and may not have a conscious patient.
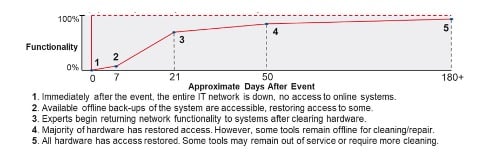
One study found that remediation efforts following data breaches left healthcare facilities less responsive, leading to excess death. The time required to order and conduct an electrocardiogram for potential heart attack patients increased by up to 2.7 minutes, and mortality increased by 36 deaths per 10,000 heart-attack patients, during the three years following a breach, according to a paper published in Health Services Research.
In addition, while cyber-physical concerns are more present in businesses — especially in the industrial sector — hospitals must regularly deal with the concerns. In few other industries could a cyberattack have the dire consequences as in healthcare settings, Claroty's Greenhalgh told README.
"There's device types in the hospitals that you don't have in regular manufacturing, or the industrial setting," he said. "Medical devices ... increase the attack surface, and the regular security tools ... they don't work. They don't talk to those types of OT devices the way they do with IT devices."
A more comprehensive approach to protecting healthcare is necessary, experts agree. Already, the Biden administration has established cybersecurity performance goals for critical infrastructure in 2021, including healthcare, and launched its National Cybersecurity Strategy earlier this year, which puts more onus on device makers to secure their products. And, in August, the administration, along with the Advanced Research Projects Agency for Health (ARPA-H) has launched a search for better cyber defenses for healthcare systems.
The industry and patients need as much support as possible, Blackberry's Bestuchev told README.
"As long as each hospital, each organization inside of healthcare, is literally working on its own, to defend itself — that's not a good strategy, we have seen it's not good," he said. "So there needs to be a collective policy that can be enforced to protect healthcare from the bottom to the top."
Until healthcare facilities are well protected, their systems — and human lives — will continue to be at risk.