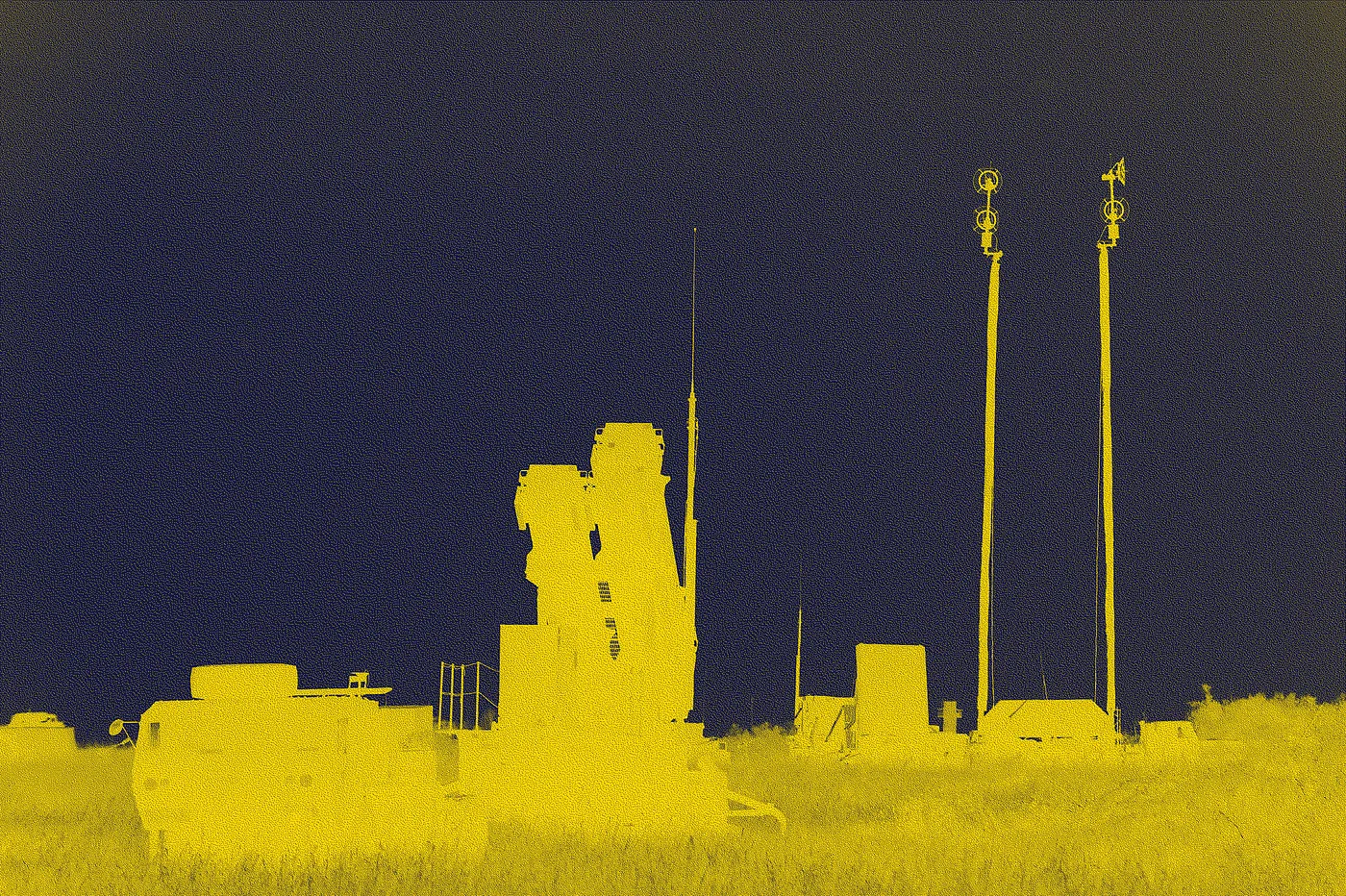
A trove of emails from top Homeland Security officials expose how the U.S. government scrambled to ensure the defenses of American utilities after Russia brought down parts of Ukraine’s power grid in 2015.
Welcome to Changelog for 2/13/22, published by Synack! I’m your host, Blake. From some pretty serious Apple patches to a disheartening update on the Log4j vulnerability’s long tail, last week’s threat level was tomato.
Blake here, reporting from Washington. It’s been another jam-packed week for cybersecurity news, with a massive crypto heist, a first-of-its-kind NSA interview and some gloomy numbers for a Pentagon supply chain security program.
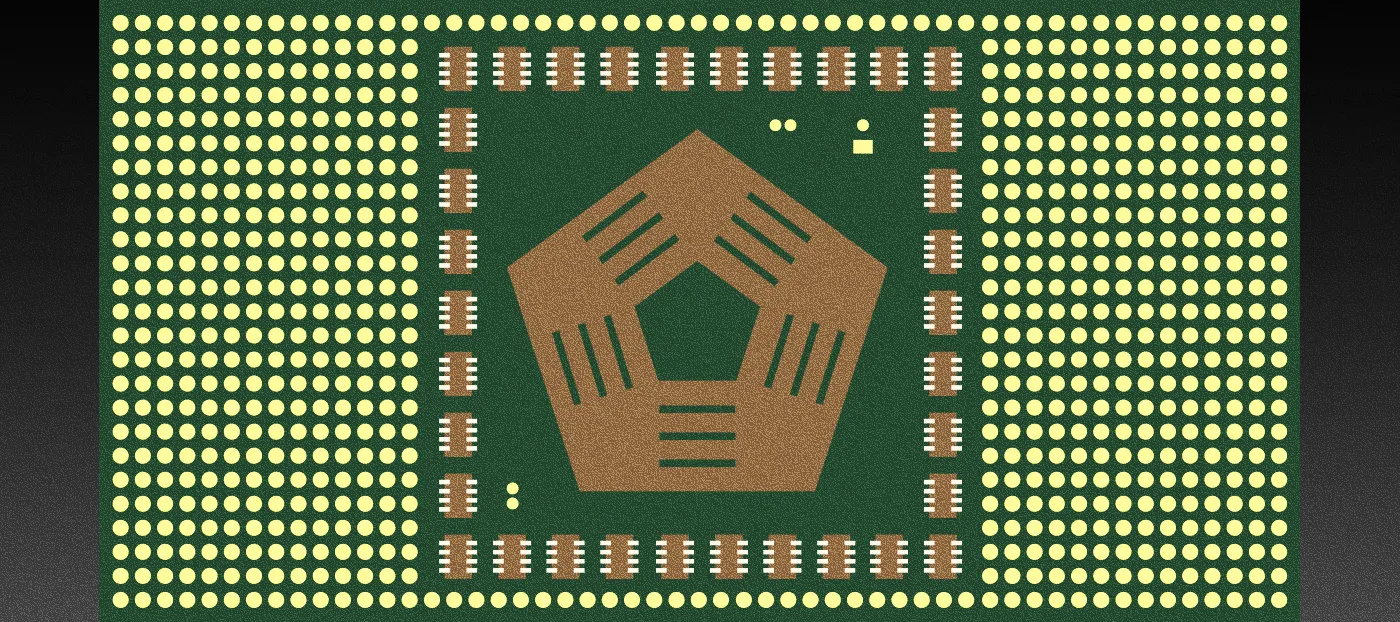
The Biden administration is forging ahead with a scaled-back plan to regulate cybersecurity in the vast and complicated defense industry marketplace. But the halting rollout of the Cybersecurity Maturity Model Certification, or CMMC, program illustrates the perils and pitfalls of rewriting supply chain cyber rules for the defense industrial base.
Go inside one of the most technically challenging bug bounties ever with the researcher who subverted secure hardware designed by MIT and the University of Cambridge.
Welcome to Changelog by README! I’m your host, Blake Sobczak. Every Sunday, I’ll deliver cybersecurity news and analysis to your inbox, provided the internet hasn’t gone down in flames.
A team of North American researchers is developing a statistics-based technique to weed out falsehoods from social media platforms, with implications for election integrity, cybersecurity and COVID-19.
The WhisperGate malware masquerades as ransomware but really breaks computer files beyond repair.
The second annual Hack-A-Sat competition pits security researchers against real satellite equipment as the U.S. military rushes to address space cybersecurity risks.